2020 was a hacker’s dream. Overnight, millions of Americans traded in business casual for sweatpants, and peace of mind for fear and uncertainty. The result? A 715% increase in ransomware attacks compared to 2019 (per Bitdefender).
In this article, we will discuss the rise of double extortion attacks, why COVID-19 created a perfect landscape for cybercrime, and finally, how companies can best protect themselves moving forward.
Pre-Pandemic: The Rise of Double Extortion
The first documented ransomware virus, known as the AIDS Trojan or PC Cyborg, was created in 1989 by evolutionary-biologist Dr. Joseph L. Popp. Leading up to the World Health Organization’s International AIDS Conference in Stockholm, Sweden, Popp gained access to an event mailing list, and distributed more than 20,000 infected floppy disks to potential attendees.
The disks, labeled “AIDS Information – Introductory Diskettes,” contained malicious code that locked files and demanded victims send $189 to a PO Box in Panama if they wanted to unlock their data. Experts quickly created decryption tools to beat Popp’s virus, but the damage was done; in 1989, digital extortion was born.
Ransomware attackers became more and more sophisticated over the next 30 years, but their end goal remained the same… encrypt files and demand a ransom to unlock them.
Companies began to grow more aware of their extortion exposure and created digital and physical backups of critical data to mitigate the hacker’s negotiating power. Then everything changed in 2019 with the introduction of Maze Ransomware and “double extortion.”
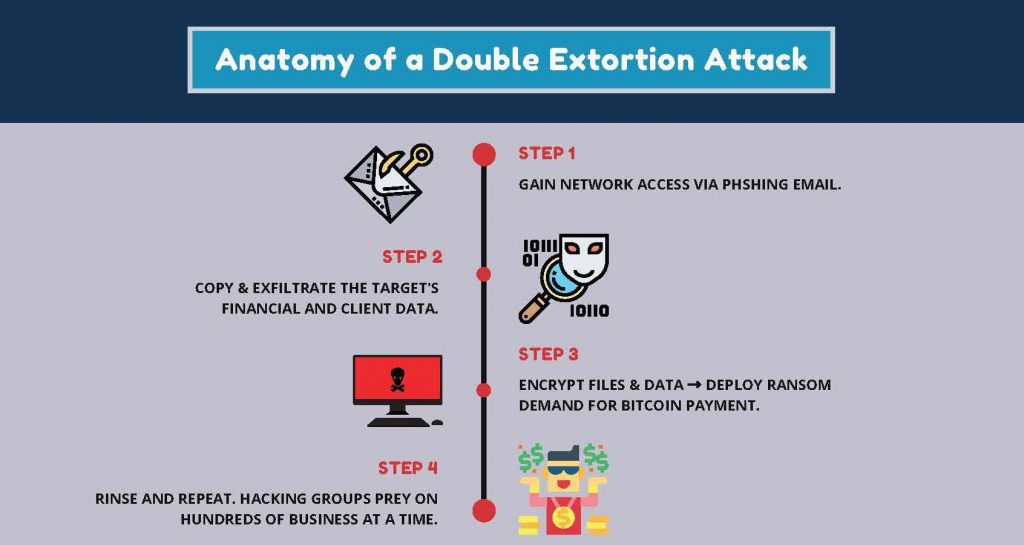
Maze, the first ransomware strain known to exfiltrate private data before encryption, was discovered in May of 2019 by Malwarebytes Director of Threat Intelligence Jérôme Segura.
Before encrypting the victim’s files, this strain copied and exfiltrated as many files as possible, giving hackers an unprecedented leg up in negotiations. You don’t want to pay our ransom demand? Fine, we’ll expose all your clients’ personal information onto the dark web.
These attacks, which picked up steam exponentially during the second half of 2019, introduced a massive new layer of costs to ransomware victims in the form of increased reputational harm and wide-scale privacy violation fines and penalties.
Then Comes COVID-19: A Perfect Storm
The rapid shift to remote work environments played a massive role in the ransomware spike during the pandemic, but not for the reasons most would assume. The most valuable asset to hackers was not people’s use of unsecured home wi-fi networks or their transition to using personal devices for work… it was good old-fashioned fear and uncertainty.
Preying on fear had two major advantages for hackers in 2020. First, it provided perfect subject matter for phishing campaigns. According to cybersecurity firm KnowBe4’s Q1 2020 Top Clicked Phishing Report, 4 of the most used phishing email subject lines related in some way to COVID-19 and the changes that came with it. The top subject lines from the report:
- PTO Policy Changes
- Test of the [[company_name]] Emergency Notification System
- Revised Vacation & Sick Time Policy
- CDC Health Alert Network: Coronavirus Outbreak Cases (this was a wide-scale campaign sent from spoofed CDC email addresses)
The second huge advantage to the uncertain environment created by the pandemic was that it made businesses much more likely to pay ransoms quickly, as business downtime and interruption were especially scary as many sectors of the US economy were coming to a screeching halt. Because businesses were more likely to pay ransoms to get operations back running ASAP, hackers became more and more brazen with the amounts they began to demand.
Coveware found that the average ransom demand during 2020 was $111,605, up more than 30% from Q4 averages in 2019. For even more context, the average ransomware demand in 2018 was a measly $5k.
Early data from 2021 shows that ransomware continues to be the #1 cyber threat to American businesses.
Protect yourself from the financial burden of a cyber-attack. Contact us today at 818-302-3060.